TIPS #12: Breaches are inevitable. How can companies use cyber insurance to manage financial risk?
Shane Shook
December 20, 2023
- Blog Post
- TIPS
Issue: Every company is going to get breached or compromised at some point.
Even the best cyber defenses can’t stop every threat.
It’s true that preventing cyber attacks from becoming breaches (and breaches from becoming compromises) should be the top cybersecurity priority for every company. As shown in previous TIPS posts, organizations can identify and protect critical business resources with a mix of active and passive defenses, fine-tuning security tools with policies that address relevant risks.
However, all companies will likely experience a breach or compromise, regardless of their security posture. This may be due to unknown vulnerabilities, human error (like falling for a social engineering attack or alert fatigue within the SOC), or insider threats. Recent incidents like the 3CX and MOVEit supply chain breaches (and subsequent compromises) also show how the interconnected digital landscape increases attack surfaces and the likelihood of a breach.
Impact: A breach or compromise can be expensive and disruptive, especially if you’re under-insured.
When attacks are successful and evolve into breaches and compromises, companies face a growing number of impacts. Recovery is often a multi-faceted process with costs including legal and breach coach fees, PR expenses, ransom payments, forensic analysis, identity remediation for customers, and lost revenue from business disruption (usually the single biggest expense). These expenses add up: the average breach costs $4.5 million ($9.48 million in the United States).
Cyber insurance coverage acts as a form of financial risk management to limit losses and speed up recovery. It lowers overall costs, improves the likelihood of data recovery, and prevents longer periods of business disruption.
Action: Invest in posture management, cyber insurance, and incident response and recovery to reduce financial risk.
1. Prioritize an active security posture to lower risk and reduce insurance premiums.
A well-aligned security posture lowers the likelihood of a breach or compromise and helps your company respond quickly to incidents. Active defenses lower risk and can reduce the cost of your cyber insurance premiums as well.
Bishop Fox helps companies develop a proactive application security posture and defend dynamic attack surfaces with services including penetration testing and security assessments. SolCyber helps companies with security posture management and provides active and passive security capabilities in a unified platform.
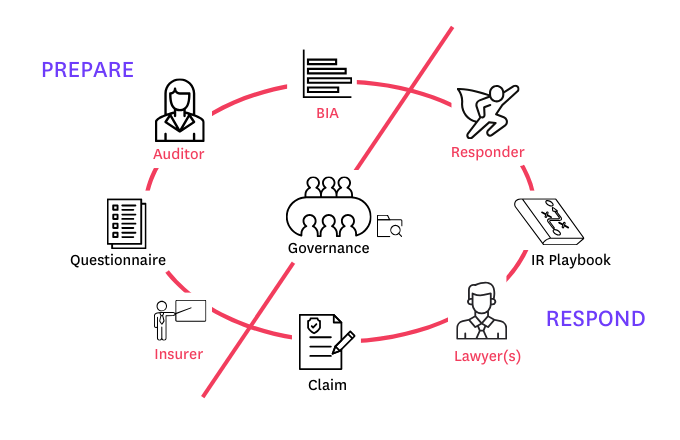
2. Use cyber insurance to curtail financial risk.
Invest in cyber insurance to protect your business and mitigate the impacts of a breach or compromise. Converge Insurance uses advanced data technology to create customized insurance solutions for their customers.
Insurers and managing general agents (MGAs) like Converge rely upon cyber risk data, analytics, and assessments to underwrite policies and provide competitive rates. CyberCube assesses enterprise security posture and provides cyber risk analytics and data to insurers and MGAs. Constella Intelligence generates actionable identity intelligence to protect enterprises and help insurers and MGAs set rates.
3. Implement an incident response and recovery plan
Incident response (IR) and recovery is critical following a breach or compromise. Surefire Cyber helps companies create a comprehensive IR plan and determine the scope of recovery and remediation after an incident. As a case manager and panel provider for leading insurance carriers, they can help you reincorporate damaged systems and tools, reduce costs, and build a more resilient security program.